This post may contain affiliate links. I only recommend products I use and love. Read the full disclosure here
Updated on: December 16, 2025
Originally published on: December 16, 2025
Most organizations know encryption is important, but the pace of change can make planning feel risky. Quantum computing turns long-term threats into present-day design decisions, which is why a post-quantum encryption strategy is becoming part of responsible security planning. The smartest move is to start early, reduce guesswork, and adopt a roadmap that evolves as standards finalize.

The Quantum Risk Is A Now Problem
Adversaries can capture modern traffic and decrypt it later when quantum attacks become feasible.
That means the shelf life of protected data matters as much as the modern threat model. If records must stay confidential for 5 to 10 years, you need a plan that begins now, not when hardware headlines arrive.
Build A Practical Transition Plan
Create a lightweight program that spans architecture, engineering, vendors, and compliance. Midway through that plan, include a clear step on adopting quantum secure encryption for cryptography in your security strategy, then tie it to timelines, pilot owners, and success metrics. Close the loop with quarterly reviews so lessons feed the next wave.
Map each initiative to a single accountable owner so decisions move quickly and roadblocks surface early. Break large transitions into small, testable milestones that deliver visible progress without overwhelming teams.
Document dependency risks so sequencing issues do not stall downstream work. Use lightweight dashboards to track adoption, friction points, and operational impact in real time. Align training cycles with each phase, so staff gain the right skills just before they need to apply them.
What The New Standards Change
Post-quantum algorithms are no longer experimental for planning purposes.
National standards bodies have finalized families for general encryption and signatures, and they have urged administrators to begin transition work. This stability lets you budget, test, and phase upgrades without betting on speculative tech.
Prioritize Data And Workloads
Start with a confidentiality horizon. List datasets that must remain secret the longest, like health records, legal archives, and customer keys.
Protect long-life data first, then move to systems with high availability needs, then to internal apps with shorter exposure windows.
- Tag long-retention data and bind stricter deadlines
- Map where cryptography is embedded vs. configurable
- Separate pilots for data at rest and data in transit\
- Track vendor dependencies and upgrade paths
- Define rollback triggers and capture test evidence
Modernize Keys, Protocols, And Inventory
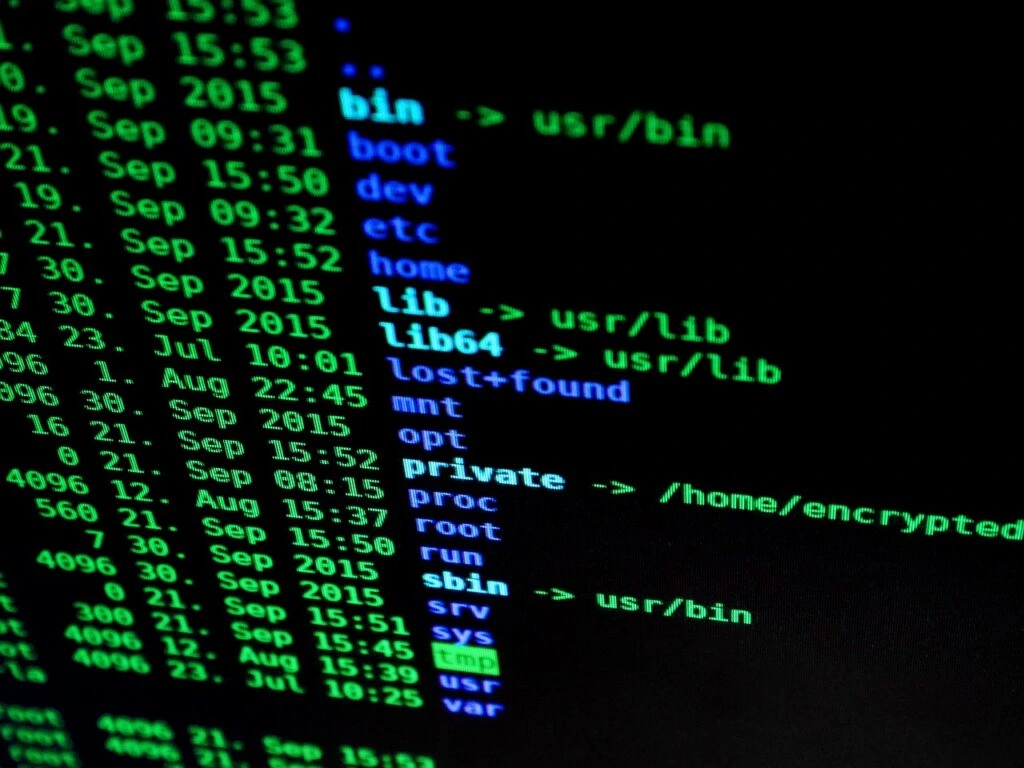
Inventory is the foundation. A federal cybersecurity agency advises cataloging every place public-key cryptography appears, from TLS and VPNs to code signing and email. Treat that list as a living asset, not a one-time audit.
Rotate keys more frequently, shorten certificate lifetimes, and prefer algorithm agility so you can swap primitives without redesigning systems. Where supported, test the hybrid key exchange that combines classical and post-quantum components to hedge early in the rollout.
Update Data At Rest Without Disruption
Encrypting stored data is mostly about safe re-keying and performance. Pilot post-quantum options for database links and object storage gateways, then measure CPU impact and latency under real workloads.
Use rolling migrations with dual-write or snapshot-and-rehydrate patterns to avoid downtime. Document how keys are generated, wrapped, stored, and rotated so audits and forensics can follow the chain.
Strengthen Network And Application Layers
For data in transit, upgrade TLS libraries, validate ciphers, and allow negotiation paths that support next-gen algorithms. At the application layer, refactor custom crypto to remove hard-coded choices and centralize operations in a vetted module.
Replace homegrown protocols with well-reviewed standards. Add telemetry that records negotiated algorithms, key sizes, and error modes so you can spot drift the moment a change rolls out.
Manage Vendors And Third-Party Risk
Your crypto boundary extends into partner stacks. Ask suppliers for their post-quantum timelines, supported algorithms, and evidence of interoperability testing. Require algorithm agility in new contracts and set milestone dates for pilots in non-production.
If a critical vendor lags, design compensating controls like additional application-level encryption or tokenization to reduce exposure as you wait.
Monitor, Test, And Prove Readiness
Security earns trust with evidence. Build a small dashboard that tracks coverage across endpoints, services, and data stores, plus mean time to remediate crypto misconfigurations.
Run table-top exercises that simulate certificate failures or negotiation mismatches and record what improved afterward. A well-known industry report has shown that faster identification and containment reduce breach costs, so treat speed as a control and measure it.
